It’s no surprise that dark data and unstructured content cause many challenges during migration. Companies must choose between two equally problematic options of the common lift-and-shift or a fully manual migration method. Executing a migration without knowing exactly what data you’re moving can be risky. But there is a new methodology, a third option that we call intelligent file migration.
Intelligent File Migration
Although fairly new technology, intelligent migration uses classification and sensitivity discovery technology within the context of a migration scenario. Now organizations can discover and classify unstructured data before migration.
The goal is to use information output from Intelligent Discovery to build a data governance plan and then execute an informed migration that adds structure to the existing data. This causes all data, old and new, to conform to the new plan which allows your organization to properly govern your growing volume of data.
Intelligent file migration points an Intelligent discovery engine at a content source, then identifies the document type of the content (such as an invoice, agreement, contract, etc.). Next, the engine searches that content for any potential privacy data (CCPA, CPRA, GDPR, etc.) or other corporate sensitive data. The engine can then pre-tag those documents, similar to a coin sorter. Finally, the data is migrated to an appropriate destination based on content type and sensitivity.
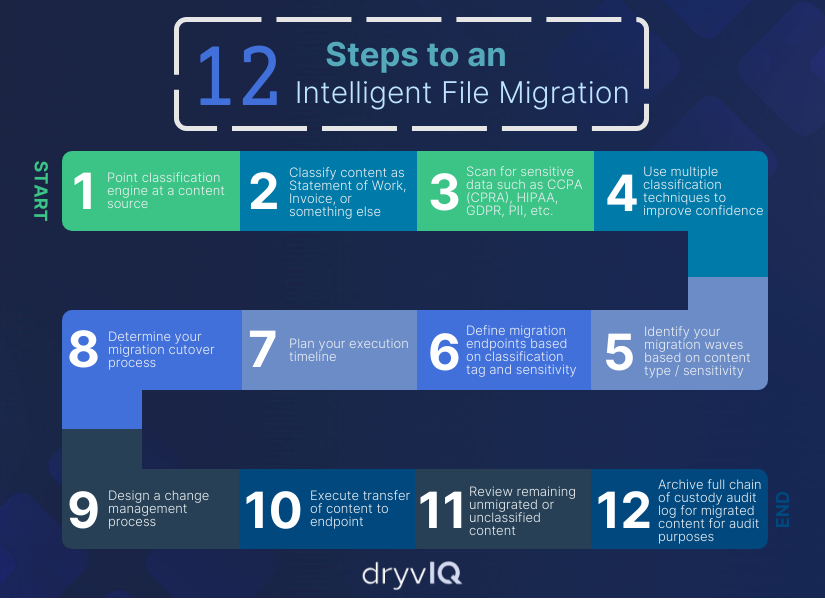
12 Steps to an Intelligent File Migration Infographic
An intelligent migration allows an organization to follow the #1 rule of data migration which is “Know Your Data” while also preventing analysis paralysis and a migration project that never ends. Follow these 12 steps to execute an Intelligent Migration
- Direct a classification engine at a content source
- Classify the document type of each file, such as a statement of work, invoice, etc.
- Scan for sensitive data such as CCPA (CPRA), HIPAA, GDPR, PII, etc. or other corporate sensitive information or intellectual property
- Use multiple classification techniques to improve confidence
- Identify your migration waves, typically based on department or collaboration
- Define migration endpoints based on classification tag and sensitivity
- Plan your execution timeline
- Determine your migration cutover process
- Design a change management process
- Execute transfer of source content to appropriate destination endpoints
- Review any remaining non-migrated or unclassified content
- Archive full chain of custody audit log of migrated content for audit purposes
Learn more about Intelligent Data Migration:
What Intelligent Data Migration Is – And Why You Need It
[Video] Advice to Organizations Considering Intelligent Data Migration
DryvIQ’s approach to Intelligent Migration
Insurance Company Makes a Carve-Out Acquisition Requiring an Intelligent Carve-Out Data Migration
Aerospace Acquisition Requires Moving Google Workspace Content to Microsoft 365