Data Loss Prevention
Understanding why data loss prevention is so essential is a matter of understanding the true impact that data loss can have on a company. With companies like Facebook, Google, and Amazon all having net worths in the hundreds of billions of dollars, it is safe to say that data is a valuable commodity. Any company in any industry collects massive amounts of data and regardless of what that company does with their data, they need to ensure that it is kept safe and out of unauthorized users’ hands. When attempting to gain a grasp of the implications of data loss on a company, it is imperative to understand both the type of data that can be lost and the type of loss that can happen.
In essence, organizations need to wrestle several data-related factors;
- How do they classify their data?
- What data do they need to keep?
- How do they regulate access to that data?
- How do they ensure that the data they keep don’t get
- lost,
- misused,
- accessed by unauthorized users, or
- exfiltrated.
The systems and procedures to manage these data issues fall into managing data loss prevention (DLP). The outcome is that DLP is now a mission-critical component of every aspect of a company’s IT and security posture.
What is the Impact of Data Loss?
While all data is sacrosanct, some data is more valuable. Consider, for example, general personal identifiable information (PII) or financial data that the payment card industry collects (PCI). Within that scope of data, there are tiers of data. A first name that becomes obviated from PII data may not trigger an audit. However, the sudden loss of obfuscation on social security numbers, another data type also classified as PII, on even a moderate scale, can result in negative media coverage and heavy fines may be levied. Evidence of this is no further than the Equifax settlement of $575 million to FTC in 2019.
Data loss can impact a company’s bottom line in several different ways, even when fines or sanctions are not levied. If PCI data gets accidentally deleted, the least of a SaaS company’s worry is losing the ability to run recurring credit card payments.
Similarly on the theme of sales, any company that has been in business for a while and collects data on their prospects has a leg up on their competition. And the value of this data is enhanced when a company layers machine learning and AI onto its sales data. The more information they have, the more accurate their predictions are. On the flip side, if vast swaths of data are lost, misplaced, or otherwise go missing, the company can lose its competitive edge. In more sinister circumstances if a competitor acquires that data, they can quickly capture significant market share without a significant investment in acquiring the virgin data.
Implementing Data Loss Prevention
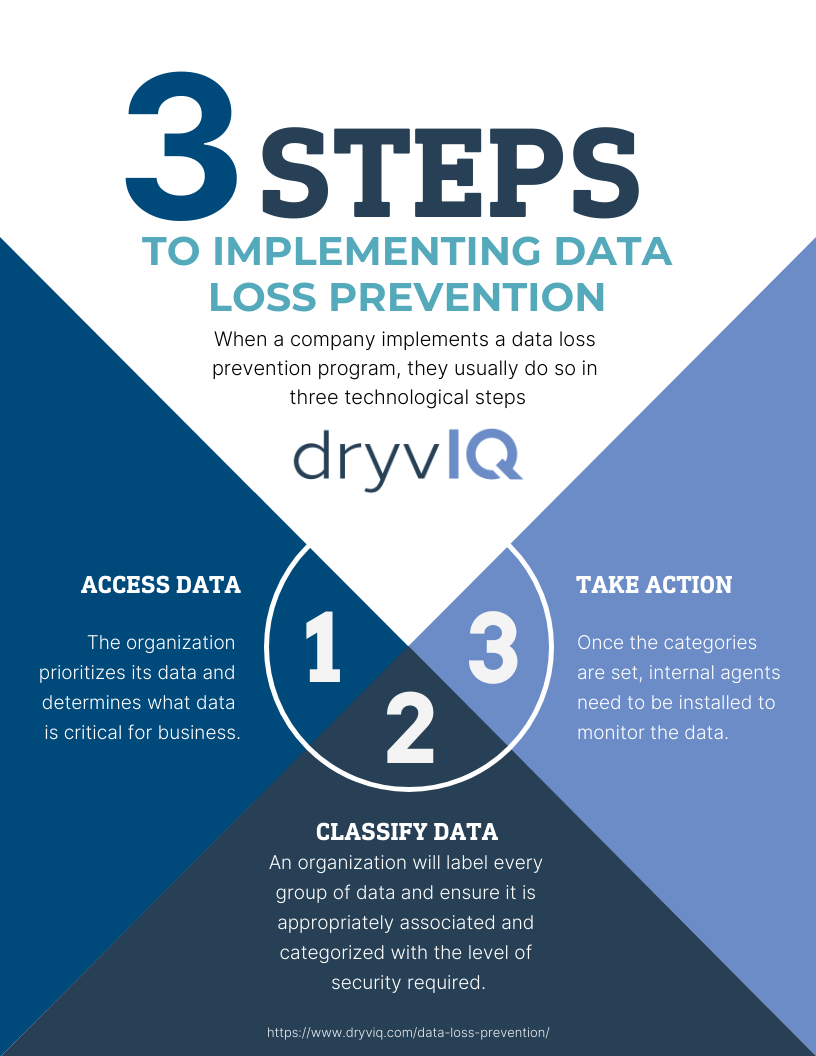
When a company implements a data loss prevention program, they usually do so in three technological steps that follow what was outlined above:
Accessing Data
In this step, the organization prioritizes its data and determines what data is critical for the business. These data may be essential to the business (such as sensitive institutional data). It may be data that, if lost or adversely accessed, would cause problems (such as PII or PCI). Or it may be data related to compliance (such as HIPAA). Once an organization has identified and prioritized that data above other data sets, it can move on to the next step.
Classifying Data
Classifying the data is the step where an organization will label every group of data and ensure it is appropriately associated and categorized with the level of security required. The aforementioned high-priority data would be in the highest and most secure category. Whereas less relevant data, such as the weekly lunch menus, would be categorized much lower. One reason that classification and categorization is such a critical step is that securing and monitoring data can be costly in both time and money. Thus having lower priority data categorized as such can produce cost savings. As well, an organization can use low-priority data to fill strategically placed honeypots ensuring that any invader takes valuable time deciphering low-value data.
Acting on Data
Once the categories are set, internal agents need to be installed to monitor the data. The actions of monitoring include ensuring that the data is consistently being appropriately prioritized, classified, as well as monitored for unauthorized access.
Misclassified data, such as high-priority data being categorized as low-priority, could make the data far more easily accessible to unauthorized users. As well, if data is misclassified, it could lead to instances where it gets lost internally; who would be looking for PCI data in the same folder as lunch menus?
For these reasons monitoring data loss prevention systems is difficult and requires systematic audits ensuring that monitoring is being conducted effectively.
Once the data has been identified, classified, and an efficient monitoring system has been implemented, an effective DLP program also includes extensive training and testing of all users. Why users? Users are the largest group of people with access to the data and concurrently, users are at the largest security risk of cyberattacks such as phishing.
What Happens When Data is Lost?
The issue remains that even with proper data loss prevention policies and procedures in place, what happens when monitored systems identify data loss? The first question that must first be answered is why was the data lost; was it an intentional or an unintentional action that caused the loss?
Unintentional data loss happens through activities such as routine backup, archiving, and deletion of older files. This is why the identification and classification of files are critical. Older files that contain sensitive data may need to be disposed of in a particular manner that may also require an audit trail or chain of custody. On the other hand, it’s likely safe to delete PDF images of lunch menus from 1993.
Intentional data loss may be the result of a mistyped line in an algorithm by an IT manager that was intentionally looking to delete files but swept up many critical ones in the process. A more sinister backstory could be an exfiltration due to a cyberattack and some data went missing.
In either case, the faster someone is notified of the data loss, the better. Once notified, the data loss prevention team needs to get in gear and take charge. Typically the DLP does this in three steps; identifying where and when the data was lost, identifying what data was lost, and then resecuring the remaining data.
When Was the Data Lost?
The first step is identifying where and when the data was lost. Regardless of whether the data loss was intentional or not, the root cause needs to be identified.
- Was the data loss due to a process that is persisting?
- Or something that happened that one time?
- Was the data loss precipitated by a process that will turn back on again?
An organization must address all of these factors prior to moving on to the next step. Like in a ship, if you cannot fix the hole, it doesn’t matter how much water you can bail out; you’re still sinking.
What Data Was Lost?
The second step is identifying the data. While a breach is a breach, knowing what data has been leaked or lost is vital. Perhaps there was an exfiltration attempt, but the hacker only found the honeypot. Great, lock it down, resecure your endpoints, and move on. If it was PCI or HIPAA compliance data, proper authorities need to be notified quickly. Typically there are timelines for letting outside sources know that can help mitigate any civil violations. Know your rights.
Secure the Remaining Data
The final step is (re)securing your data and (re)testing your monitoring systems. Any time there has been data loss, the probability of a second loss is typically high. For this reason, it is imperative to review your organization’s data loss prevention policies and procedures, investigating if any areas should be shored up. As users are the weakest link in any DLP program, some notification and possibly remedial training may be in order.
Conclusion
As data is more and more ubiquitous and its value rising daily, implementing measures and systems for data loss prevention is key. Every time a user accesses, updates, or moves data, the possibility of misclassifying the data allows for potential unauthorized users to access it. Or worse, the data could be lost. Therefore organizations should keep a close eye on data and users’ use of data. A company that does not take its data security seriously runs the risk of losing control of its data. A company that loses control of its data will quickly lose significant market share due to any number of factors.
Infographic: 3 Steps to Implementing Data Loss Prevention
By Mark Shalinsky at Data Sales Science.